Template
Hi guys, please find the link below to the google document which shows the report which can be sent to people to let them know their website is vulnerable. There are many website still vulnerable to this issue. I am providing a template report which can be used to disclose to sites to help you get started. If you contribute to it or improve or report successfully please do let me know!
https://docs.google.com/document/d/1rdpLTE5Dgt0ofYGgB6_J0YdICBj_xgVMuu6hrpGLWac/edit?usp=sharing
Based on original template from Andy Gill: https://github.com/ZephrFish/BugBountyTemplates
Background
This vulnerability has been present for some time, however, it had been noticed by a security researcher recently, Larry Cashdollar who has since reported it as a CVE (aka Common vulnerability and Exposure). This is so the wider security community can check for this in the future and warn website owners, but as a side effect it has given it press and media exposure.
Although the hacker community has known about this for some time, as there are YouTube tutorials (Youtube, 2018). These may now gain more exposure and make it easier for hackers to learn how to undertake such attacks. These videos cover how to exploit the vulnerability and upload code, which can compromise the security of your company.
Issue Description
Through the use of some scripts, arbitrary code can be uploaded to a server, (Mitre.org, 2018) This means that someone can upload nefarious scripts to a company’s server and have it compromised. This can happen if the server is using Blueimp jQuery-File-Upload and is running a vulnerable version. Blueimp was created Sebastian Tschan (Github-BlueImp, 2018)
A working Proof of concept attacking code has been released and now is publicly known within the offensive security community. (Github – lcashdol, 2018)
The code in https://github.com/blueimp/jQuery-File-Upload/blob/master/server/php/UploadHandler.php doesn’t require any validation to upload files to the server. It also doesn’t exclude file types. This allows for remote code execution. (VapidLabs, 2018)
This affects versions prior to v9.22.1, v9.22.0 was created June 20th 2018 anything before this date is vulnerable and possible for remote code execution.
This has now received press exposure making it more likely that you will be attacked. Videos have existed online for some years, but only has been reported as a CVE now.
Video demonstration of the attack being used in the wild can be seen here: https://youtu.be/E7RAHgM0inc (Youtube, 2018)
Affected URL/Area
You need to be aware that the Apache configuration settings can interfere with the security of the Blueimp file-upload code. Please see below explanation of this.
The PHP implementation of Blueimp file-upload restricts uploaded files by default to image files (GIF, JPEG, PNG). This has previously been undertaken with the use of a .htaccess file.
The PHP implementation stores uploaded files in the pre-defined directory files. This directory contains an .htaccess file with directives for Apache to enforce file type restrictions.
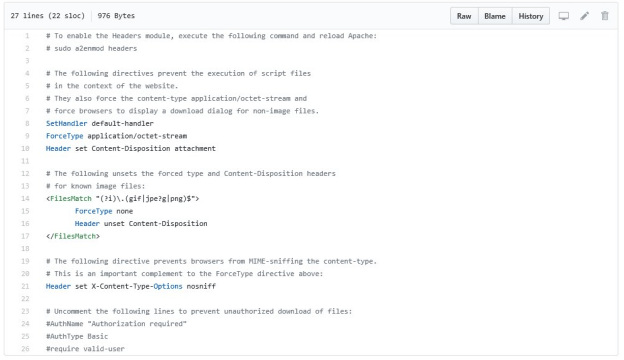
Image of .htacccess file included within https://github.com/blueimp/jQuery-File-Upload/blob/master/server/php/files/.htaccess
However since Apache version 2.3.9, .htaccess support is disabled by default and must be explicitly enabled with the AllowOverride directive. Therefore the .htaccess file created by Blueimp is ignored by default.
Without the configuration in the .htaccess file working, it allows uploads of all file types makes your site vulnerable to remote code execution attacks.
In version 9.2.21=> a security fix has been applied. One area this is carried out is within the jQuery-File-Upload/server/php/index.php file. It now includes a accepted file types by default, to help mitigate this issue.
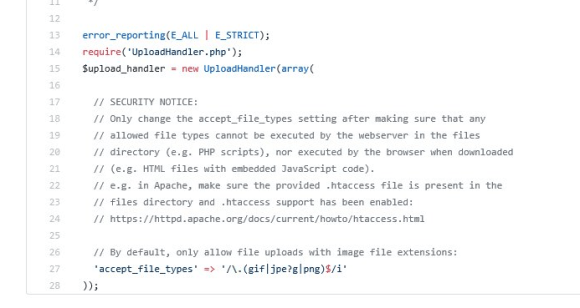
Image of ameded Index.php file included within https://github.com/blueimp/jQuery-File-Upload/tree/v9.23.0
Impact
- Possible full compromise of a server via uploading scripts.
- Compromise of server could result in effect on the confidentiality, integrity and the availability of the website and the server.
- This is now public knowledge as it has hit the news recently. I was able to find the code running on many sites through some simple searches. Nefarious attackers will now be doing the same, although it has been known to be used in the wild for some time.
- Please read the media reports regarding this, ZDnet recently reported and showed videos with regards to its impact. (ZDnet, 2018)
- YouTube there are many videos demonstrating the hack, which would require medium skillset to undertake. That would mean the risk to a website is more likely to occur now it has had press exposure.
- Your customers data could be at risk, and would be a breach of GDPR / Data Protection acts for other countries.
Steps to reproduce/PoC
Exploit Code: 1. $ curl -F "files=@shell.php" http://localhost/jQuery-File-Upload-9.22.0/server/php/index.php 2. 3. Where shell.php is: 4. 5. <?php $cmd=$_GET['cmd']; system($cmd);?> Or 9. https://github.com/lcashdol/Exploits/tree/master/CVE-2018-9206
Affected Demographic/User Base
The website itself and its users.
Recommended Fix
Update code to latest version, carry out security configurations correctly and check up on the file upload functions, by the use of the exploit script.
Disable plugins that are using this version of the code.
References
Github-BlueImp. (2018). Retrieved from https://github.com/blueimp/jQuery-File-Upload
Mitre.org. (2018). Retrieved from http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-9206
VapidLabs. (2018). Retrieved from http://www.vapidlabs.com/advisory.php?v=204
ZDnet. (2018). Retrieved from https://www.zdnet.com/article/zero-day-in-popular-jquery-plugin-actively-exploited-for-at-least-three-years/